Kaseya VSA Breach – Consequences of Security Failures
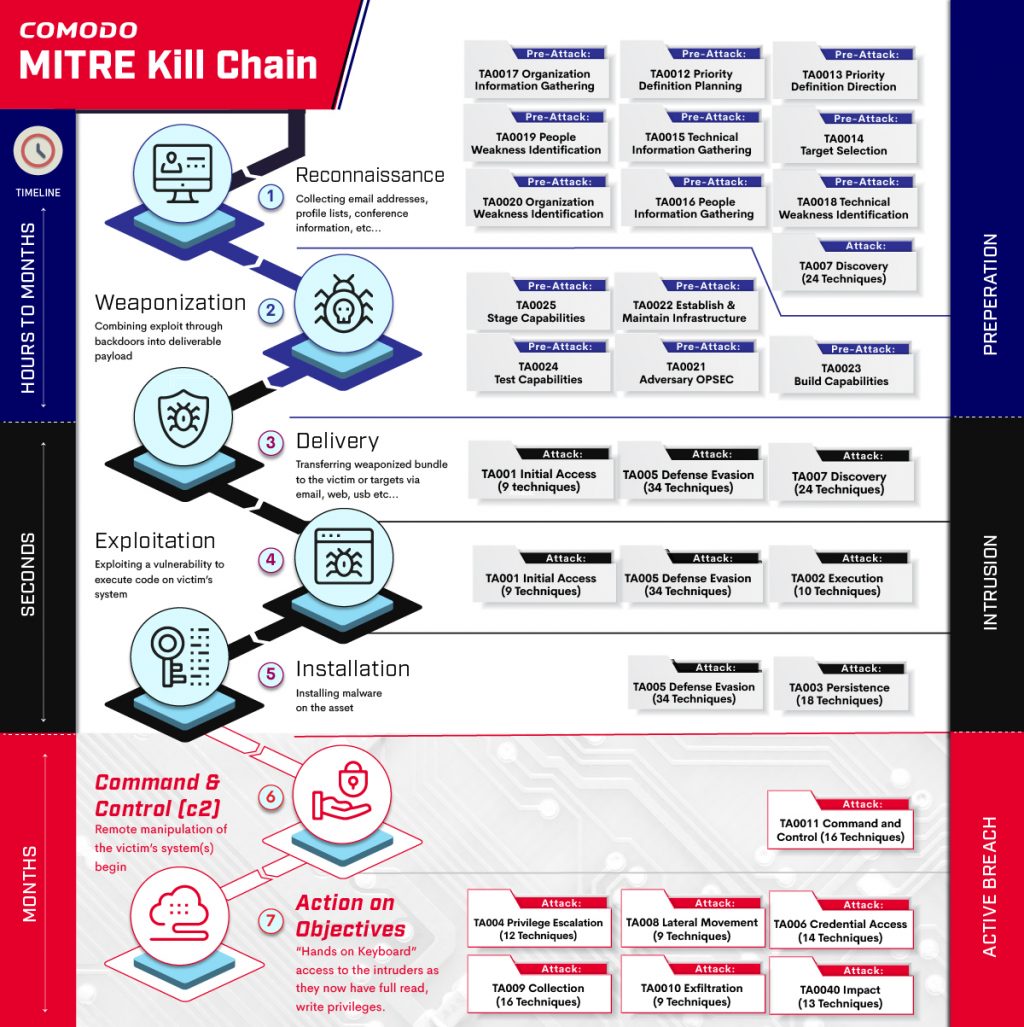
The world has witnessed another large-scale cyber-attack. On July 2, 2021, Kaseya, an IT Systems Management software firm, disclosed a security incident impacting their on-premises version of Kaseya’s Virtual System Administrator (VSA) software. The result was up to 1500 companies being held hostage to a significant ransom demand. Incidents such as these are becoming more commonplace. We are seeing…
Read more

Recent Comments